Available for preorder on Amazon.com!
Got Hacked?
- Want to be able to defend your application from hackers?
- Want to know the history of hacking and defenses against hackers?
- Want to learn to hack other other web applications?
- Want to make money on the side as a bug bounty hunter or pen tester?
The reader needs no security background - yet by the end of this book will have the fundamental skills required to begin hacking modern web applications, or defending their applications against modern hackers.
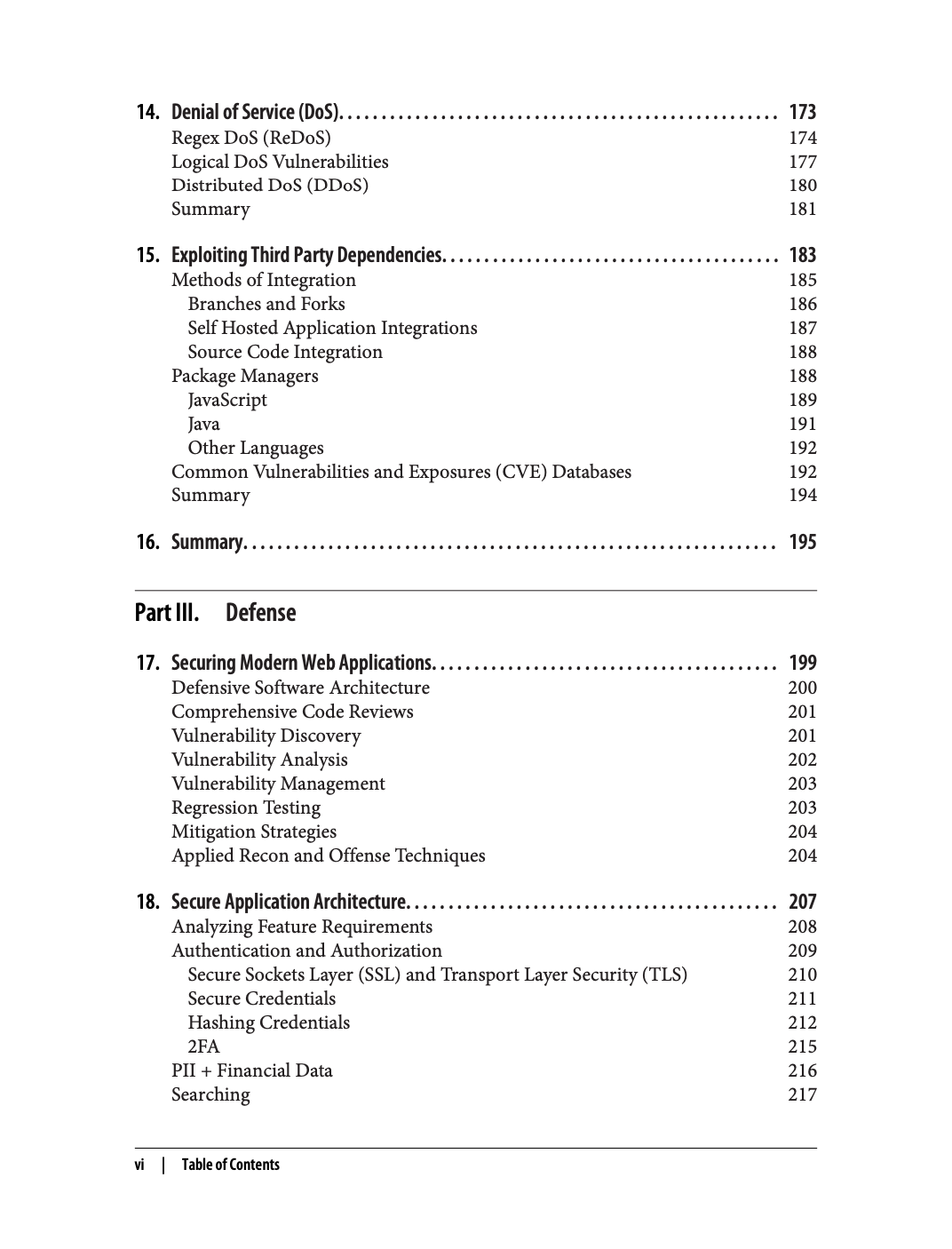
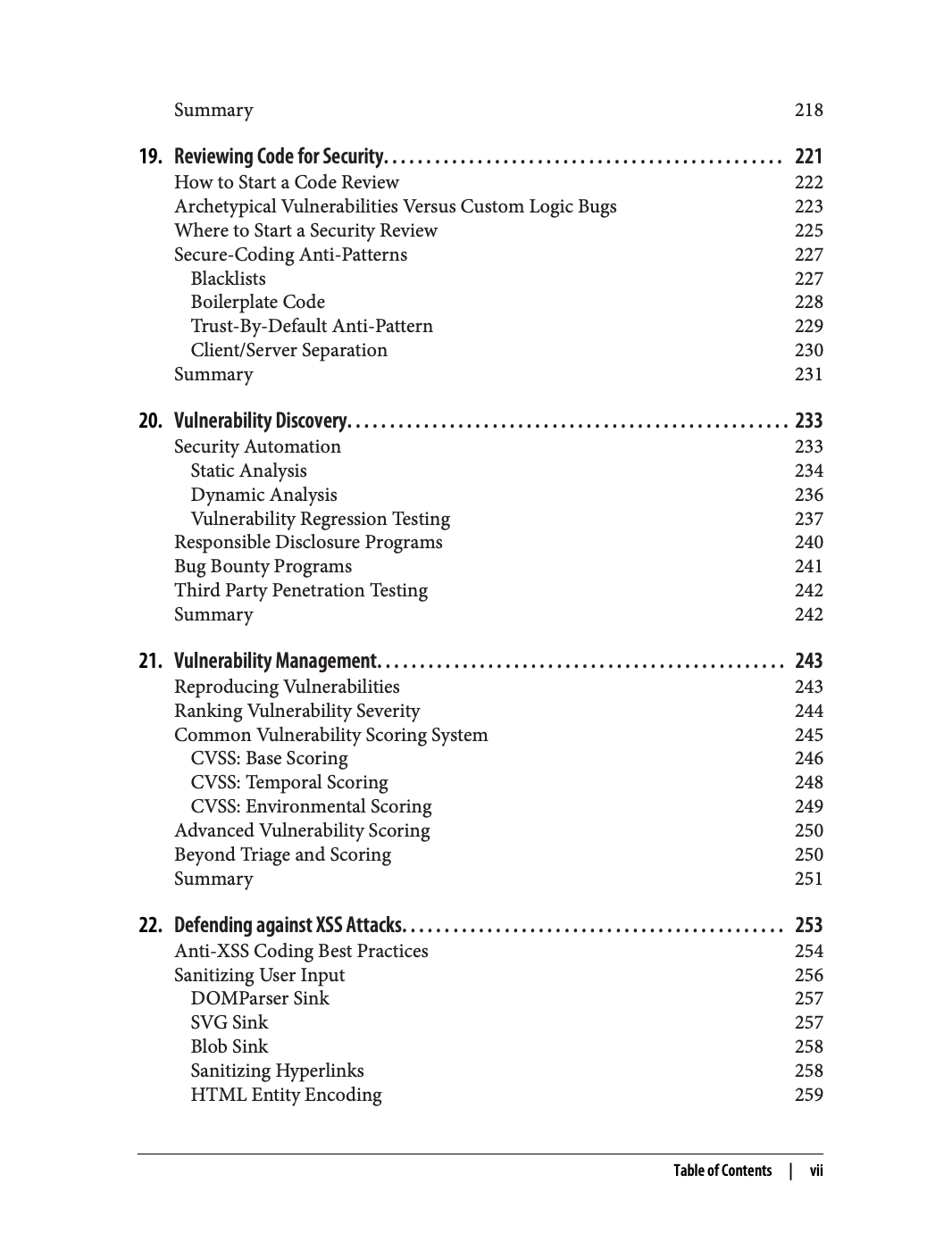
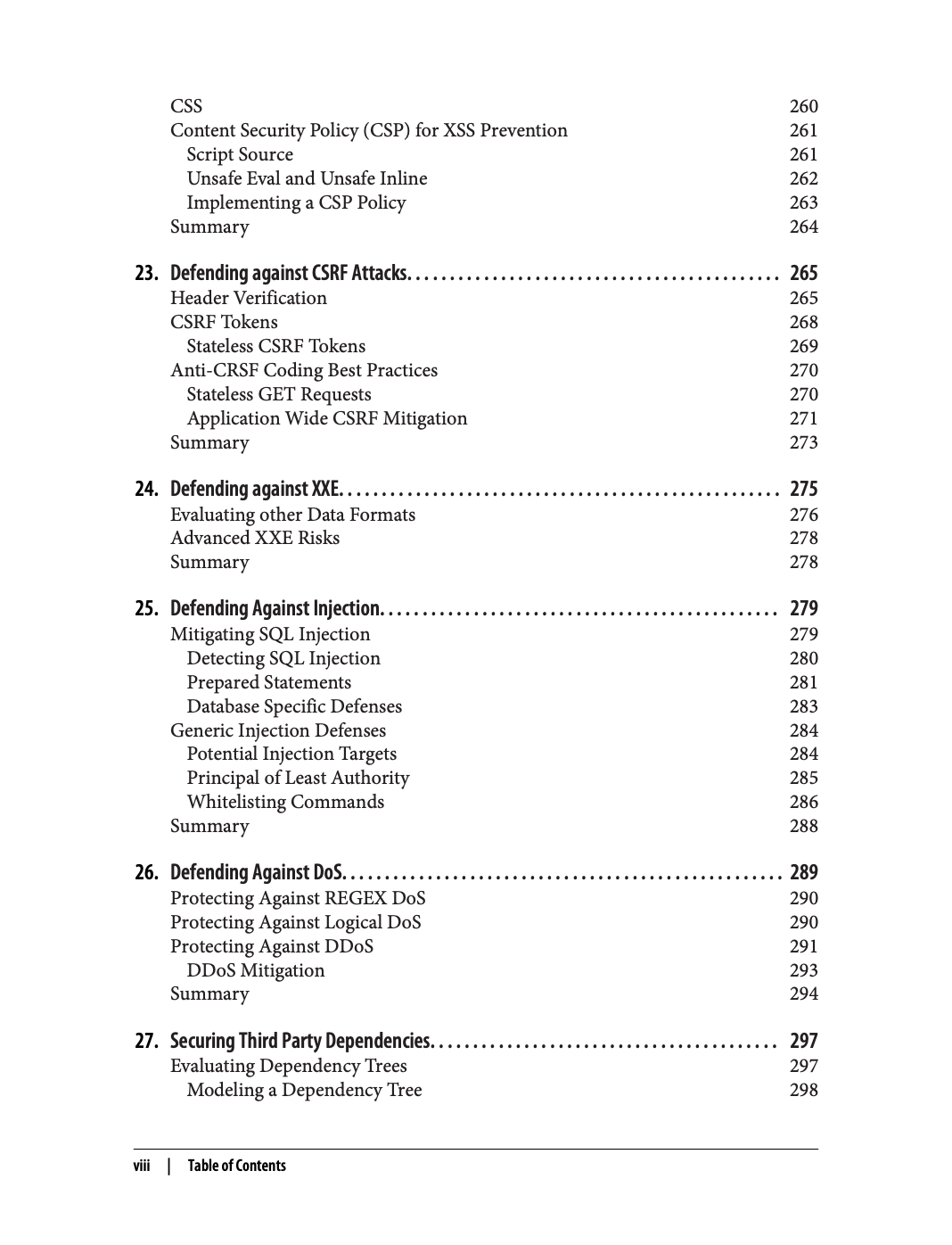
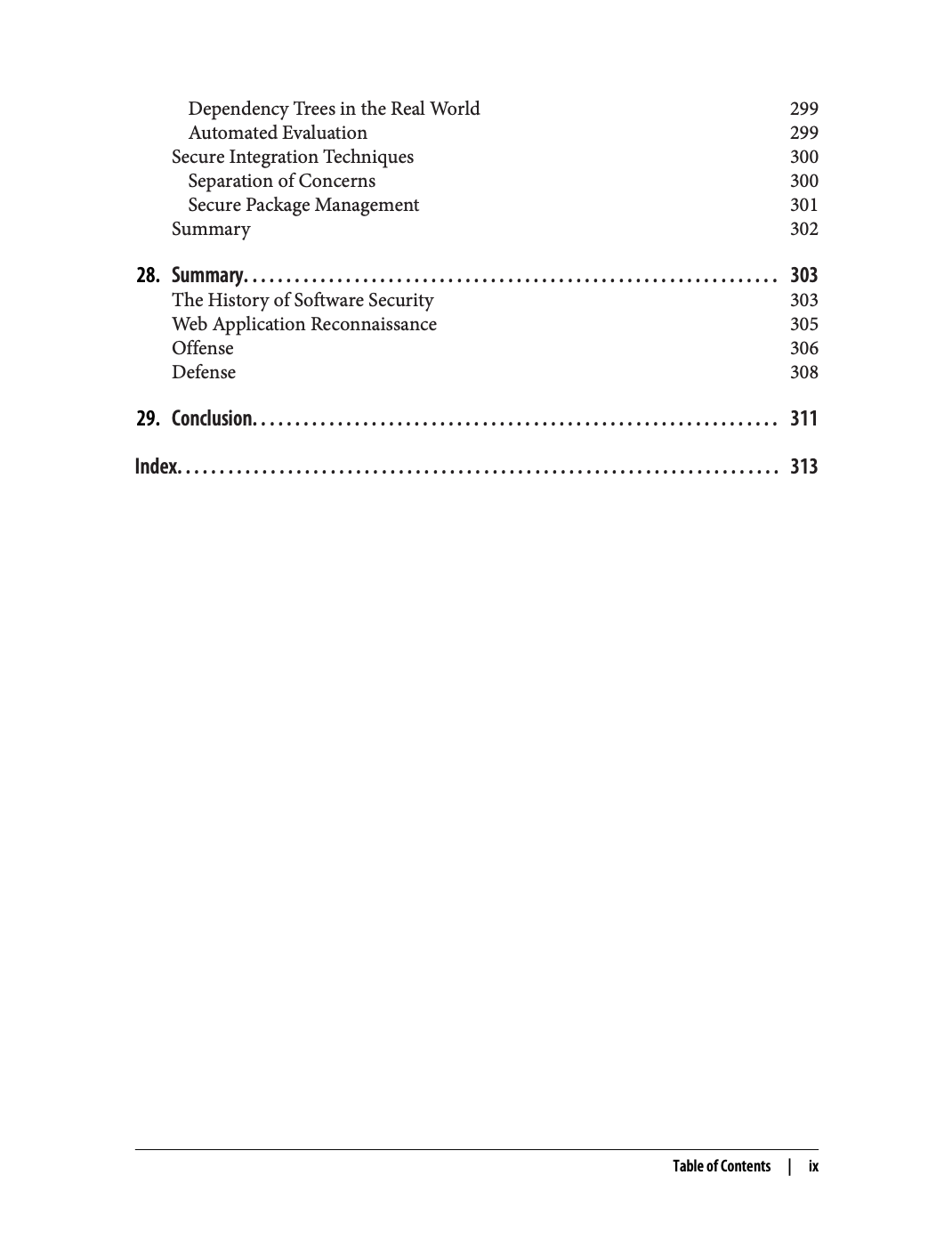
This book is structured such that each chapter carefully builds on top of the previous, eventually integrating recon, offense and defense techniques together into a full-stack security skillset.
Buy now for $49.99* Early access eBook available on Safari